InsForge Auth now supports custom SMTP providers and a built-in email template editor.
Plug in any SMTP server — SES, Resend, Postmark, Mailgun, a self-hosted Postfix — and rewrite the HTML and subject line for every auth email.
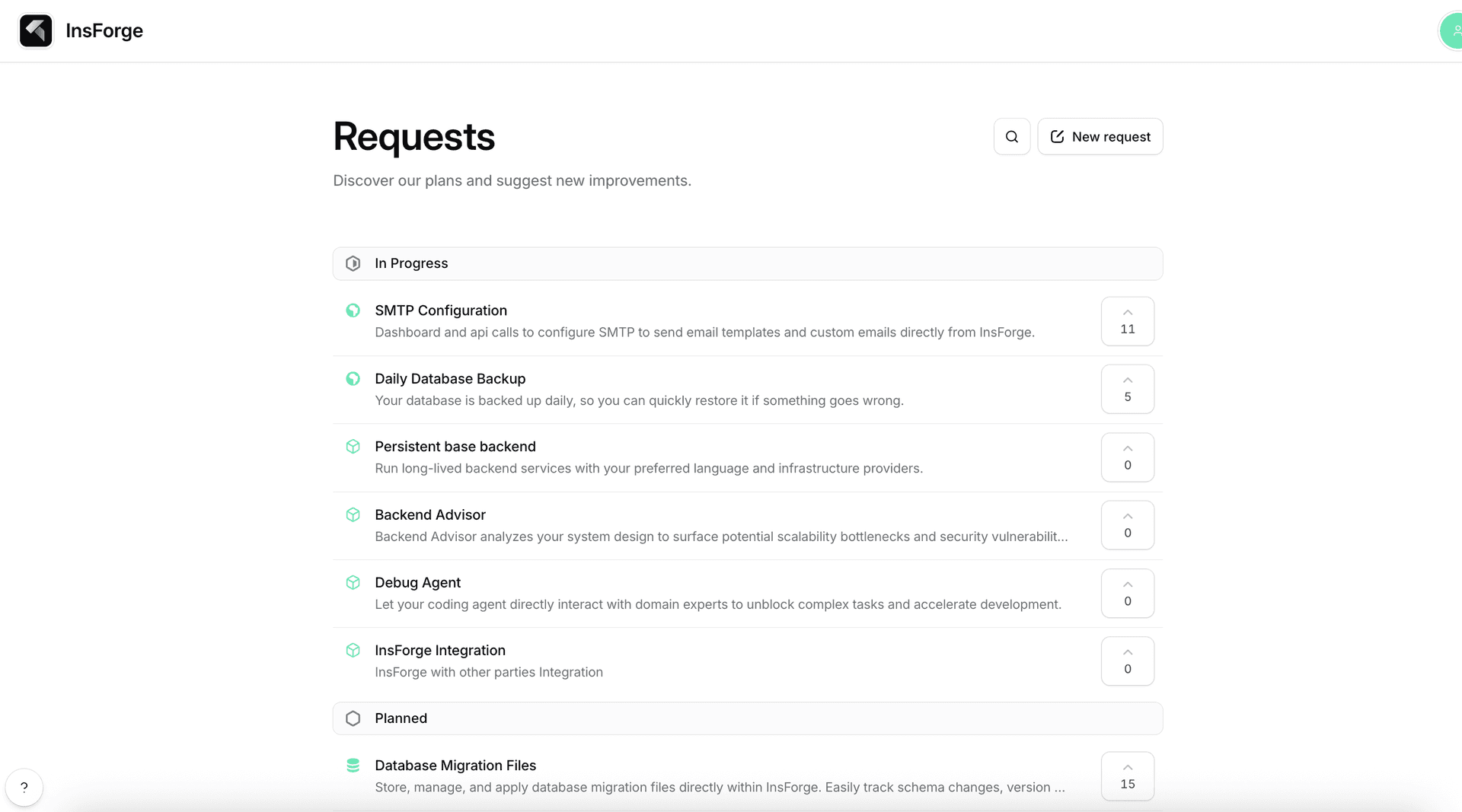
SMTP configuration was the top-voted request on our public roadmap, so this one shipped because users asked for it.
What's New
A new Custom SMTP page under Authentication in the dashboard.
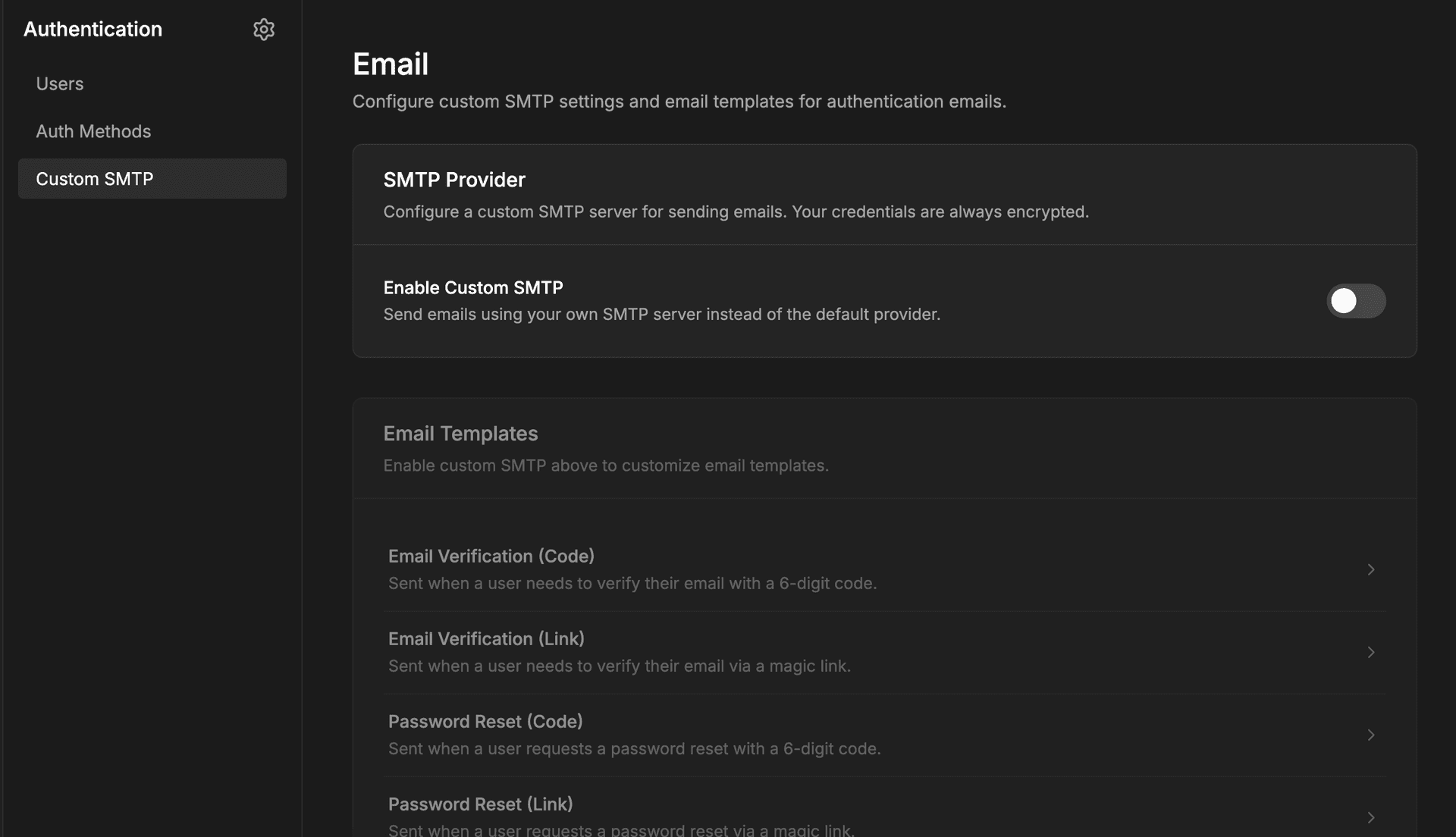
- SMTP configuration: enable toggle, sender name and email, host, port, username, password, TLS mode. InsForge validates the connection against the real server before saving.
- Template editor: pick a template (verification code, verification link, password reset code, password reset link), edit the subject and HTML body, preview in a sandboxed iframe.
Both cards are available to project admins on cloud and self-hosted deployments.
How It Works
EmailService resolves the provider per call. If an enabled SMTP config exists, mail goes through SmtpEmailProvider (built on nodemailer). Otherwise it falls back to the cloud provider. SMTP credentials live in email.smtp_configs; templates live in email.email_templates, one row per type.
Template variables — for code templates, for link templates — are HTML-escaped at render time, so a crafted display name or reset link cannot inject script into the body.
Security
- Encryption at rest: SMTP passwords are stored with AES-256-GCM and masked in API responses.
- Live verification:
transporter.verify()runs on save, so bad credentials or unreachable hosts fail before the first send. - SSRF protection: the host resolves and is checked against private and loopback ranges before a connection opens.
- Per-recipient rate limit: a 60-second minimum interval to the same address shuts down mail loops.
- Admin-only routes with audit logging on every mutation.
Configure
Open Authentication → Custom SMTP in the dashboard, enable the toggle, fill in the SMTP fields, and save. Either the connection succeeds or you get the exact SMTP error to fix — credentials, port, or DNS — before going live.
Then open the template editor and edit the four auth templates as needed.
Application code does not change:
await insforge.auth.signUpWithEmail({
email: 'user@example.com',
password: '...',
});
await insforge.auth.resetPasswordForEmail('user@example.com');
Get Started
If you are already using InsForge Auth, open Authentication → Custom SMTP and point it at a test SMTP endpoint to see the save-time verification and template editor in action.
